SBS 2003 is really a great product. It is slick, extremely easy to manage, and cheap enough for any small business. One feature in particular that small business owners continue to praise is the SBS 2003 backup wizard. It is so simple to use that “anyone” can work their way through the prompts and end up with a server that is going to magically back itself up and be error free.
You see, SBS Backup goes through each backup after creating the .bkf file and verifies it. For the most part this is great, but it unfortunately starts to break down when backup sizes start approaching 300 GBs.
Recently I was dealing with a client, and their backup had hit 276 GB. It was taking over 18 hours to complete and was becoming an unmanageable nightmare. Server performance was abysmal. How was I to cope?
Well, by default, the SBS 2003 backup utility doesn’t give you the option to turn verification off. It is simply not built into the wizard. But I wasn’t willing to give up the slick reporting features of SBS and the automatically generated and emailed server performance report…so I went in search of an answer. I needed to turn verify off to speed things up!
The SBS 2003 backup utility is based on NT Backup, but unfortunately, you cannot simply go in and change the options in the launch string as you would normally. This string is actually created on the fly before each backup by a little .exe file called bkprunner, which is located in %system root%\programs files\windows small business server\backup. This file is the key to getting the verification turned off. So, here’s the deal.
Create a folder and copy this file into the folder. Do not touch this. This will be your backup should the modified file become corrupt while making changes. Then, place another copy on your desktop.
Go onto the internet and find yourself a good, free, hex editor. There are a kazillion of them out there, and they all accomplish the same task.
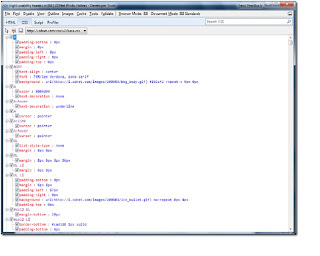
Now open this file in your hex editor and go to the hex address $113a. It is at this location that the word yes is coded into the file in hex and you will see the word yes in the unicode section. This is the “yes” which turns verification on. So, all we need to do now, is simply enter the word no…so starting at this location simply enter the following HEX string.
6E 00 6F 00 20
Save the file and you are done.
Now, if you still need more performance improvements, there are lots of other switches that can be modified in this same fashion. I would recommend giving Google a go and seeing what else you come up with.
Cheers