Firewall: The name says it all – this little piece of software (or hardware as it may be) is designed to keep your computer and the fires outside at some distance from each other. It is an essential service, yet the eagerness of some to let the fires inside and burn their houses down is not unappreciated.
Let’s face it – firewalls can be a real pain in the butt and the one that comes with windows is sometimes nearly unbearable. I know a lot of you out there are tempted to live with this particular warning message forever…..
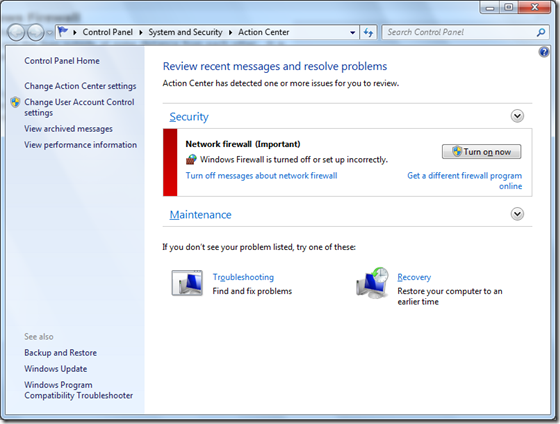
I know I certainly have, but actually the windows firewall is very easy to work with. Let’s discuss some ways that we can make this work for you.
Now first and foremost, any configuration you do to Windows firewall should be done through the firewall wizard itself. This often grabs any exceptions that are needed and most of the time will actually pre-emptively warn you when Windows firewall is blocking out something important. Don’t ignore these messages when they pop up – think about what they mean and either allow or ignore as you see fit. This will save you a lot of time.
Now, after you have tried forwardding ports as they appeared in the wizard/notification area and have failed in making the troublesome service or application work, the second step is to enable logging on the Windows firewall. Far too many people take a non-logical approach to troubleshooting firewall issues and basically just start clicking randomly allowing and denying until their issue is magically solved. Unfortunately, they have also magically opened up numerous attack surfaces on their machine and by two am the next day an army of botnets has already been able to compromise their machine and they are inadvertently relaying thousands of Cialis ads per day…this definitely puts one in between a rock and a hard place. The moral of the story here is simple: AVOID THE IMPULSE TO RANDOMLY DISABLE/FORWARD PORTS IN WINDOWS FIREWALL. Troubleshoot these systematically.
Here’s how to enable logging:
1. Open the Windows Firewall with Advance Security snap-in, right click on the firewall and choose properties.

2. Select the profile you wish to troubleshoot.
3. In the logging group, click on customize.
4. More often than not, you will be looking for dropped packets as these are the data packets that windows firewall has rejected and are probably the reason why that undocumented and proprietary software package you are trying to make work is failing. Click on yes for the dropped packets. Or, conversely, click on Yes to monitor which packets windows firewall is allowing through.

5. Click OK to apply the settings. As you can see above, the log files are kept in the system32\logFiles directory.
Now try to recreate the problem and see if Windows firewall is in fact the culprit. You will want to disable the logging after you are done with it though, as there is a considerable performance hit associated with this as the log only stores the last 4 KB of data.
Now there is one other tool that is often overlooked in tracking down port forwarding issues.
The simple netstat command when used with the –a and –b switches is a powerful tool in tracking down applications that require access to the machine or in the case of spyware blocked.
Netstat when used in this fashion will allow you to see what services and/or processes are listening for incoming packets. This, combined with a tool like process explorer by Sysinternals, is extremely useful in quickly figuring out access requirements.

With all of these tools at your disposal, there is no reason to completely disable a firewall again nor will you be forced to just click aimlessly and randomly in the firewall configuration.
Enjoy!
No comments:
Post a Comment